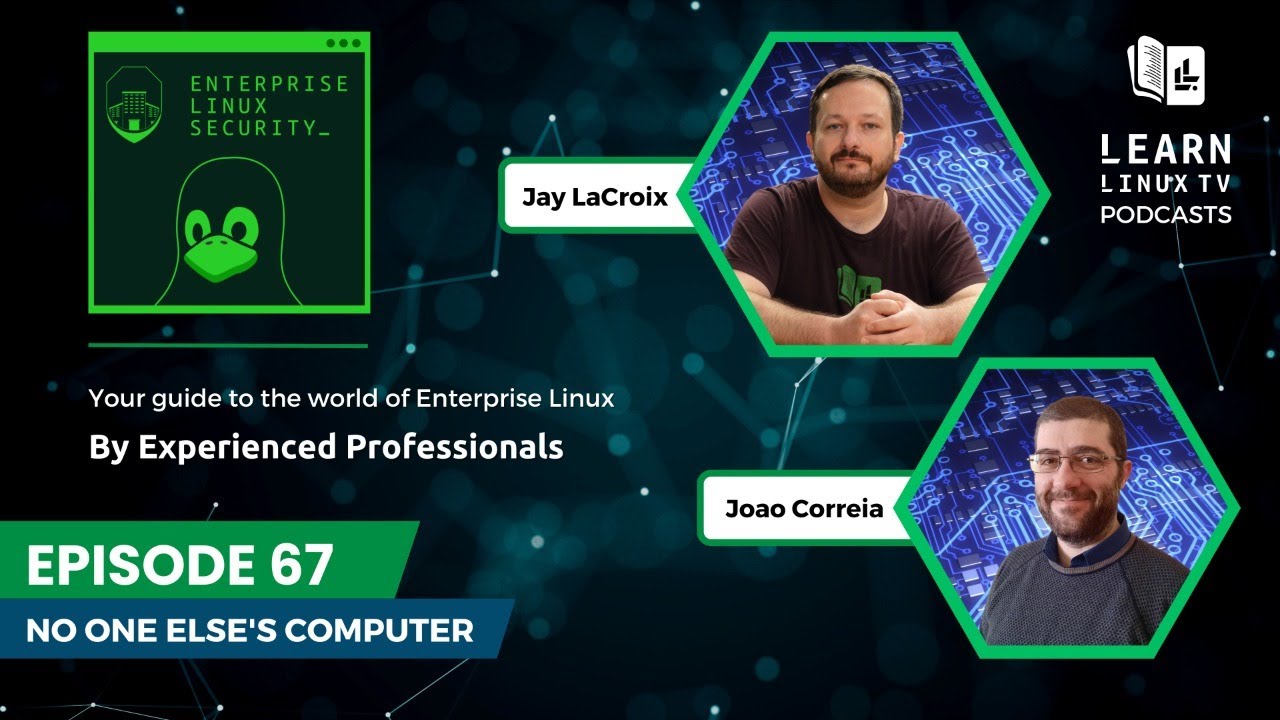
When it comes to Linux in the Enterprise, we have quite a few challenges we have to overcome on a day to day basis to ensure we can depend on our technology. We never thought Red Hat themselves would some day become our opponent, but here we are. In this episode, Jay and Joao will discuss discuss the latest impulsive and irresponsible decision Red Hat has made – as well as how that decision results in the company undermining their own customer base, while alienating the Linux Community at the same time.
Download Links
- MP3 version
- MP3 version (lower bitrate, smaller file size)
- Ogg version