In this episode, hackers clean house at Clorox (literally), Amazon has a bit of “AI privacy panic” and a weak password allowed hackers to sink a 158 year old company. Jay and Joao will discuss these stories – and more.
Relevant Articles
- Clorox Sues Cognizant After Help Desk Allegedly Gave Away Passwords to Hackers
- Amazon AI Privacy Panic — Bee Brings Bezos Panopticon
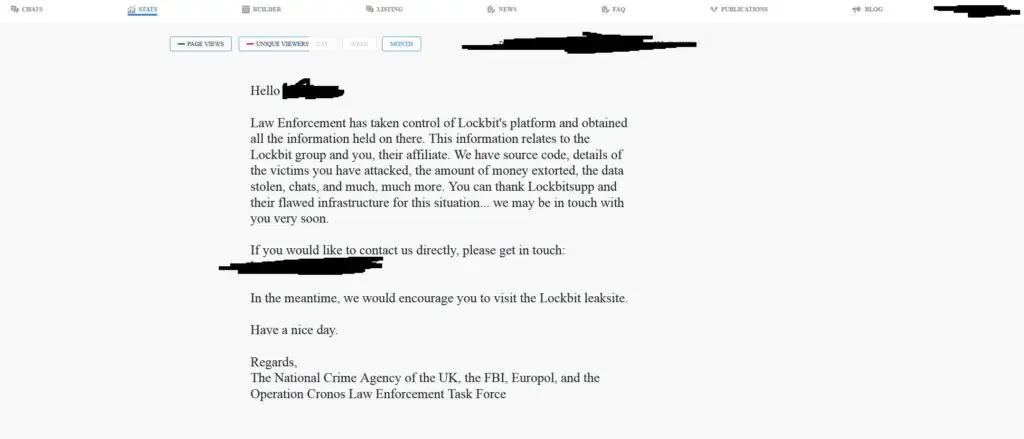
- Weak password allowed hackers to sink a 158-year-old company